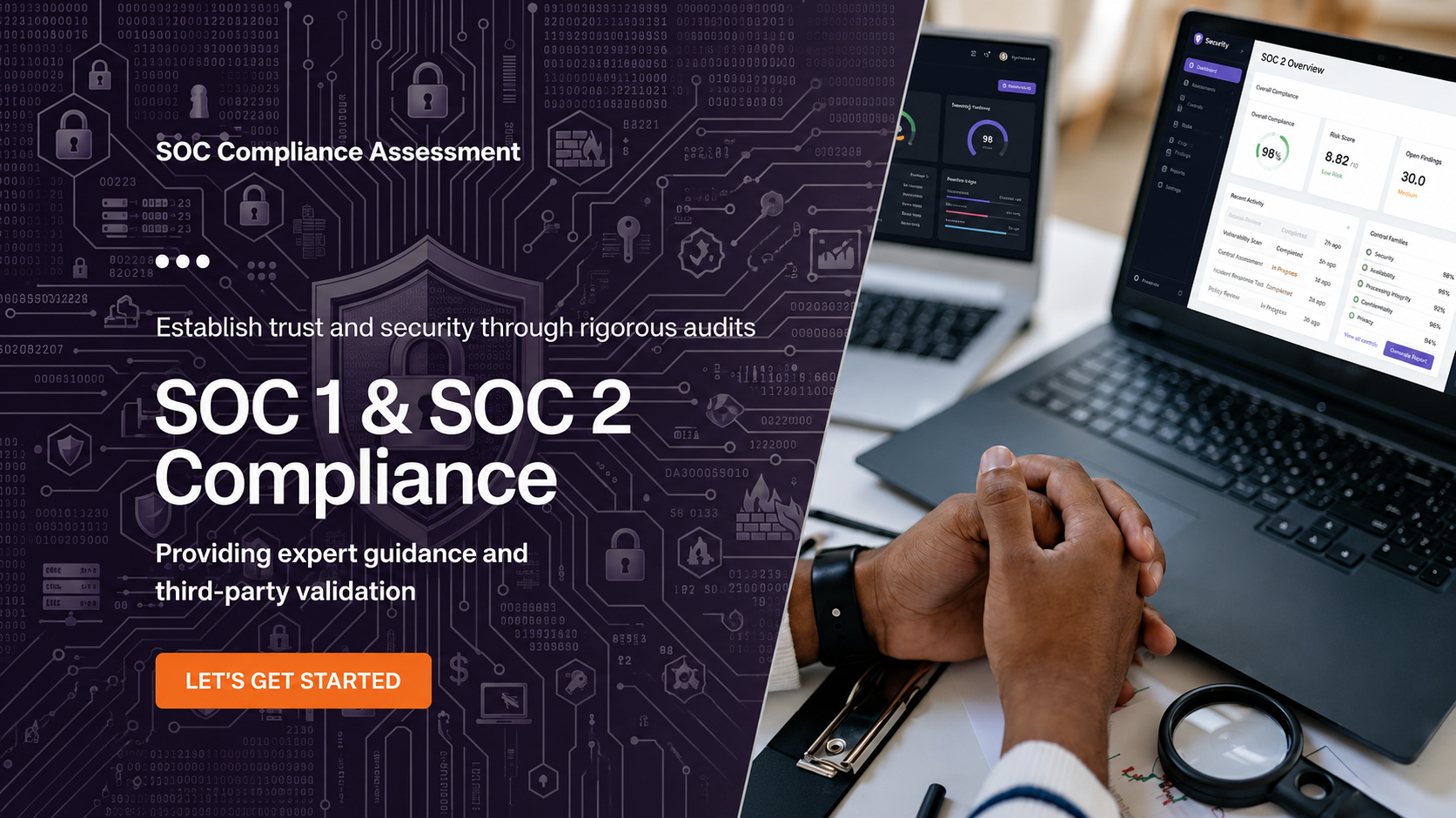
In the modern digital economy, data is a company’s most sensitive and valuable asset. For service organizations—especially SaaS providers and cloud-based firms—proving the integrity of their data handling is no longer optional. It has become a commercial necessity. The gold standard for this level of assurance is the soc 2 audit, a rigorous evaluation that demonstrates an organization’s commitment to high-level security and operational excellence.
What is a SOC 2 Audit?
A soc 2 audit is an independent examination conducted by a licensed CPA firm. It evaluates a company’s internal controls based on the American Institute of Certified Public Accountants (AICPA) Trust Services Criteria (TSC). These criteria include:
- Security: Protection against unauthorized access.
- Availability: System uptime and accessibility.
- Processing Integrity: Ensuring data processing is accurate and authorized.
- Confidentiality: Safeguarding sensitive business information.
- Privacy: Handling personal information in accordance with privacy notices.
While “Security” is the mandatory core of any audit, businesses can tailor their scope to include other criteria based on their specific client needs and service level agreements.
The Myth of SOC2 Certification
It is a common industry slip of the tongue to use the term soc2 certification, but technically, SOC 2 is an attestation, not a certification like ISO 27001. When a business successfully passes the evaluation, they receive a formal auditor’s report rather than a certificate. However, in the eyes of procurement teams and global partners, achieving a successful soc2 certification status means your organization has met the highest benchmarks for data protection.
There are two primary types of reports:
- Type I: Assesses the design of controls at a specific point in time.
- Type II: Evaluates the operating effectiveness of those controls over a period (typically 6–12 months).
Why Does Your Business Need SOC 2 Today?
The drive toward soc2 certification is fueled by the escalating landscape of cyber threats. In 2026, enterprise clients are no longer satisfied with verbal promises of security. They demand a soc 2 audit report to mitigate their own third-party risks.
Achieving this milestone offers several strategic benefits:
- Shortened Sales Cycles: Pre-emptively providing a SOC 2 report removes the friction of lengthy security questionnaires.
- Market Advantage: Small and mid-sized firms with a soc2 certification can compete for large-scale enterprise contracts that were previously out of reach.
- Operational Discipline: The audit process forces a company to document and improve their internal workflows, leading to fewer breaches and better resource management.
The Path to Success
Preparing for a soc 2 audit often takes months of gap analysis and remediation. Many forward-thinking companies now use compliance automation tools to streamline evidence collection and monitor their controls in real-time. This proactive approach ensures that when the auditor arrives, the “certification” process is a validation of existing excellence rather than a scramble for compliance.
Conclusion
In a world where trust is the primary currency, a soc 2 audit is your most valuable investment. It transforms security from a back-office technicality into a front-facing competitive edge. Whether you call it an attestation or a soc2 certification, the result remains the same: a verified, resilient business ready for the global stage.